Intersolar: AP Systems presents single-phase hybrid inverter for balcony photovoltaics
Until now, balcony inverters were mostly simple micro inverters, with batteries integrated via MC4 connectors. A hybrid inverter should improve this situation.
Marstek unveils plug-in balcony solar with AC-coupled storage at SNEC
A new manufacturer is entering the PV market. Marstek initially focused on power banks, but is now showcasing a range of products for the booming DIY solar market, including a user-friendly, AC-coupled battery solution for balconies.
Commercial perovskite solar modules at SNEC 2024 trade show
China’s Utmo Light showcased its first full perovskite PV module at this week’s SNEC PV trade fair in Shanghai, underscoring the technology’s ongoing shift toward commercialization.
CATL presents EV battery with 1,000 km range
Contemporary Amperex Technology Co. (CATL) has shown its latest lithium iron phosphate (LFP) battery at an auto show in Beijing. The Chinese company says it has an energy density of 205 Wh per kg, almost 8% higher than the current state of the art for such batteries.
Autarco releases three-phase hybrid inverters
Autarco has developed a three-phase hybrid inverter line, featuring 8 kW, 9.6 kW, 12.8 kW, and 16 kW versions and up to four independent maximum power point (MPP) trackers, along with a European efficiency rating of 97.5%.
GCL SI to introduce carbon-tracing mechanism across entire value chain
GCL SI says it will track carbon emissions from polysilicon production to module assembly and shipping. Each module will have a QR code revealing its specific carbon emissions, protected by blockchain tech to prevent tampering. It says this will offer transparency in preparation for looming Carbon Border Adjustment Mechanism (CBAM) rules.
Fischer launches clamp-free fastening system for facade PV systems
Fischer has developed a clamp-free fastening system for facade PV systems, with a mounting solution that requires minimal gaps between modules. The company says it is simple to install and dismantle.
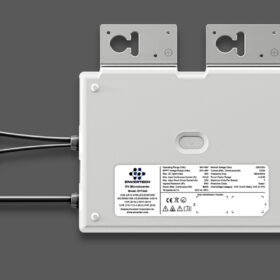
Envertech launches 800 W microinverter for residential, balcony PV
Envertech says its new microinverter has a maximum efficiency of 96.8%. The short-circuit current of the new product is 25 A and the voltage output is 220 V.
Standard Energy unveils vanadium-ion battery with 1% degradation
Vanadium offers unique characteristics as a battery material, as it can shed electrons without shifting from its ionic state, ensuring high cycling stability. South Korea’s Standard Energy has developed a battery with just 1% degradation after 20,000 cycles. The company has already completed 10 MWh of projects in its home market and now aims to expand internationally.
PV Expo Tokyo 2024: Lightweight solar modules, agri-PV and big storage aims
PV Expo Tokyo 2024, Japan’s main solar industry event, has concluded with record numbers, innovative products, and new trends. Storage auctions and new rules for power purchase agreements (PPAs) are driving the market to new spaces, as project developers scramble for land to build on, while lightweight plastic modules continue to gain prominence.