RWE drops 99.9 MW solar project in Wales on grid constraints
RWE has scrapped its 99.9 MW Butterfly solar‑plus‑storage project in Wales after determining that grid connection availability made it unviable, in a move that comes amid sharply rising connection demand and mounting pressure on the United Kingdom’s queue reform process.
European power grid investment set to rise sharply by 2027
The EU Agency for the Cooperation of Energy Regulators (ACER) says distribution grid investment has risen 51% since 2021, but warns that fragmented planning rules and regulatory distortions could limit efficiency and slow the energy transition.
Cyber threats for PV: What are credential compromise attacks and how do they work
Credential compromise attacks allow adversaries to gain unauthorized access to PV systems by stealing or guessing valid login credentials, enabling them to manipulate operations, disrupt monitoring, or take control of critical assets. These attacks can lead to operational instability, reduced energy production, and safety risks, making strong authentication and access control essential for system resilience.
Free midday electricity key to drive consumer demand to match excess PV generation
Free midday electricity schemes aim to shift household demand into periods of high solar PV generation, reducing midday surplus and evening fossil-fuel ramp-up. Research on Australia’s Solar Sharer program suggests such incentives could significantly improve renewable utilization, but outcomes depend on consumer behaviour, load shifting, and rebound effects.
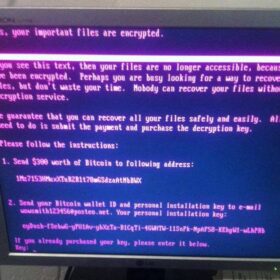
Cyber threats for PV: What are ransomware attacks and how do they work
Ransomware attacks encrypt or lock critical PV system data and control platforms, preventing operators from accessing or managing their assets until a ransom is paid. These attacks can disrupt operations, reduce energy production, and create safety risks, making robust backups, segmentation, and incident response essential for resilience.
Managing cyber risks in the era of decentralized energy
The move toward decentralized energy resources offers resilience and flexibility in power generation, but it also introduces new complexities that demand proactive security measures.
Cyber threats for PV: What are man-in-the-middle attacks and how do they work
Man-in-the-middle attacks are a serious threat to networked PV systems, allowing attackers to intercept, modify, or disrupt communications, potentially causing operational failures, physical damage, financial losses, and safety hazards. Effective defense requires a layered approach combining encryption, strong authentication, network segmentation, firewalls, IDS, and continuous monitoring to detect, prevent, and limit the impact of such attacks.
Solar PV, geothermal hybrid systems are more than niche solutions
Solar energy, driven by excellent resource conditions and rapidly improving economic attractiveness, is expected to emerge as a bulk energy supplier in future energy systems. The self-limiting effects of solar power can be circumvented through solar-hybrid solutions, such as PV-geothermal hybrid configurations.
How Switzerland plans to integrate 40 GW of solar by 2050
Swiss national grid company Swissgrid teamed up with a group of Swiss energy expects to publish a white paper covering how Switzerland can integrate up to 40 GW of solar by 2050 while maintaining safe and reliable operation of the grid.
AI-enabled hacks expose remote shutdown risk in microinverters
IT security firm Jakkaru has identified a vulnerability in microinverters from AP Systems that could enable a “kill switch” scenario, potentially shutting down tens of thousands of inverters simultaneously and disrupting grid operations.