Ransomware cyberattacks are a major category of cyber threats targeting digital and cyber-physical systems that depend on data availability and system integrity. In PV environments, where continuous monitoring and control are required, ransomware can severely impact operational continuity by denying access to essential systems and information.
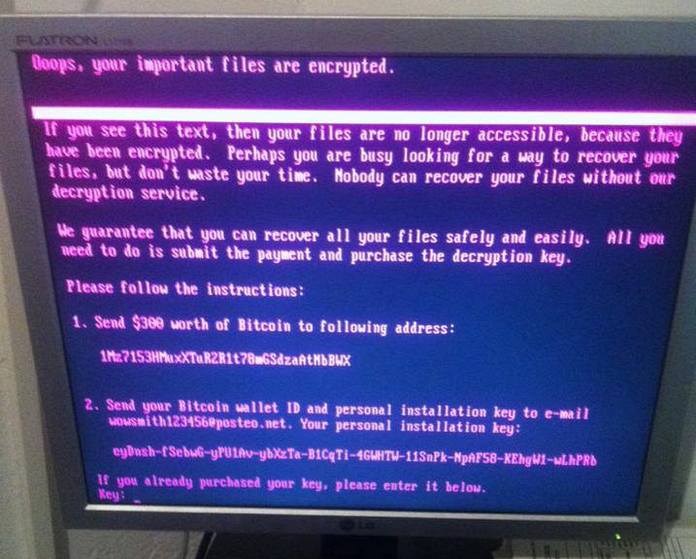
These attacks involve malicious software that infiltrates a system, encrypts files or entire platforms, and demands payment, often in cryptocurrency, in exchange for restoring access. Unlike denial-of-service attacks that flood systems or credential attacks that silently infiltrate them, ransomware directly locks operators out of their own infrastructure. As a result, operators may lose visibility and control over PV assets and associated data.
Ransomware attacks may target PV systems and solar plants by compromising monitoring platforms, SCADA systems, engineering workstations, or cloud-based management tools. Once deployed, the malware can spread across connected components, encrypting operational data, historical performance records, and configuration settings. In some cases, attackers also exfiltrate sensitive data before encryption, increasing pressure by threatening public disclosure.
Join us on Apr. 29 for pv magazine Webinar+ | Decoding the first massive cyberattack on Europe’s solar energy infrastructure – The Poland case and lessons learned
Industry experts will explore real-world cyberattack scenarios, highlight potential vulnerabilities in solar and storage systems, and share practical, actionable strategies to protect your energy assets. Attendees will gain valuable knowledge on how to anticipate, prevent, and respond to cyber threats in the rapidly evolving solar energy sector.
These attacks may also indirectly cause physical and operational risks by preventing timely control actions or fault detection. Inverters, transformers, and grid interfaces may continue operating without proper oversight, potentially leading to inefficiencies, instability, or safety hazards. Additionally, ransomware incidents can result in prolonged downtime, financial losses, and costly recovery processes.
“Ransomware attacks are a big and ever growing problem. In 2025 alone, cyber criminals generated over €800 million ($941 million) from successful attacks, according to Chainalysis, a US-based blockchain analytics company. In the PV industry, a ransom attack has the power to ‘lock up' a solar plant's ability to export power. This will cause immediate and ongoing loss in revenue, until the ransom money is paid.” Uri Sadot, Managing Director of SolarDefend and the Chairman of SolarPower Europe's Digitalization workstream, told pv magazine.
Operational modes
Ransomware attacks can operate through several infection vectors and execution methods. Common entry points include phishing emails with malicious attachments, compromised remote access services, software vulnerabilities, or supply chain compromises. Once inside, ransomware may execute immediately or remain dormant while spreading laterally across the network.
For PV systems, a ransomware attack often begins with an attacker gaining initial access to an internal network, either through compromised credentials or exploited vulnerabilities in internet-facing systems. From there, the attacker may escalate privileges, moving from low access to high control within the system, or move laterally to critical components such as SCADA servers or monitoring platforms, and deploy the ransomware payload across multiple systems simultaneously.
Common techniques in PV environments include encrypting databases used for performance monitoring, locking operator interfaces, and disabling backup systems to prevent easy recovery. In distributed solar fleets, attackers may target centralized management platforms, affecting multiple sites at once and amplifying operational impact.
Once the attack is triggered, operators may suddenly lose access to systems, encounter ransom notes, or see files rendered unusable. At this stage, the attack is fully active, and recovery becomes complex, often requiring system restoration, forensic investigation, and coordination with cybersecurity experts. In severe cases, manual operation or complete shutdown of affected systems may be necessary.
Defense
A potential defense against ransomware attacks in PV systems is to implement robust backup strategies, ensuring that critical data and system configurations can be restored without paying a ransom. Backups should be stored securely, regularly updated, and isolated from the main network to prevent compromise.
Network segmentation is another key defense, limiting the ability of ransomware to spread across systems. By isolating critical components such as inverters, SCADA systems, and monitoring platforms, operators can contain infections and reduce overall impact.
Endpoint protection tools and regular software updates can help prevent malware from executing by detecting known threats and patching vulnerabilities. Additionally, restricting administrative privileges and implementing application whitelisting can reduce the attack surface.
Intrusion detection systems (IDSs) and security monitoring tools can identify early signs of ransomware activity, such as unusual file encryption behavior or unauthorized access attempts. Combined with automated response mechanisms, these tools can help contain attacks before they fully propagate.
User awareness training is also essential, as phishing remains one of the most common entry points for ransomware. Educating personnel to recognize suspicious emails and follow secure practices can significantly reduce risk.
In summary, ransomware attacks represent a serious risk to PV systems, primarily affecting data availability, operational continuity, and financial stability. By locking operators out of critical systems, these attacks can halt operations and create cascading effects across interconnected infrastructure.
Although measures such as secure backups, segmentation, endpoint protection, monitoring, and user training can reduce the risk, no single solution can fully prevent ransomware incidents. Systems must be designed with layered defenses, continuous monitoring, and well-defined incident response plans.
This approach not only helps ensure rapid recovery from attacks but also limits the attacker’s ability to spread, persist, or cause long-term disruption across PV assets.
“The impact of ransomware on victims is particularly difficult to navigate,” Sadot conclued. “If you don't pay the ransom, you suffer losses. If you do pay the ransom, you encourage future attacks. Not an easy dilemma. And for us in the PV sector there is an added complexity. If a big company decides not to pay, massive power outages may be the result. Can anyone really afford that?”
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.




By submitting this form you agree to pv magazine using your data for the purposes of publishing your comment.
Your personal data will only be disclosed or otherwise transmitted to third parties for the purposes of spam filtering or if this is necessary for technical maintenance of the website. Any other transfer to third parties will not take place unless this is justified on the basis of applicable data protection regulations or if pv magazine is legally obliged to do so.
You may revoke this consent at any time with effect for the future, in which case your personal data will be deleted immediately. Otherwise, your data will be deleted if pv magazine has processed your request or the purpose of data storage is fulfilled.
Further information on data privacy can be found in our Data Protection Policy.