Distributed Denial-of-Service (DDoS) cyberattacks are a major category of cyber threats targeting digital and cyber-physical systems that rely on network availability, particularly when systems depend on continuous communication for monitoring and control.
These attacks involve overwhelming a target system, server, or network with a massive volume of traffic generated from multiple compromised devices. Instead of intercepting communication, as in other attack types, DDoS attacks aim to exhaust system resources, making services unavailable to legitimate users. As a result, operators may lose visibility and control over critical infrastructure.
DDoS attacks may also target PV systems and solar plants that are network-connected, disrupting communications between controllers, inverters, SCADA systems, and monitoring platforms. By flooding these systems with traffic, attackers can delay or completely block operational data exchange, potentially leading to system instability or shutdowns.
These attacks may also indirectly cause physical stress on inverters, transformers, or panels by interrupting proper control signals or preventing timely fault detection. Furthermore, they could lead to reduced energy production, and recovery costs, while also creating safety risks for personnel operating without real-time system visibility.
“DDoS attacks are especially risky for BESS operators. A BESS plant relies on real time communications with the grid to participate in stability markets. A DDoS attack will effectively jam those communications with senseless noise. This will impair the plant's ability to generate revenue, sometimes without you even knowing about it” Uri Sadot, Managing Director of SolarDefend and the Chairman of SolarPower Europe's Digitalization workstream, told pv magazine.
Join us on Apr. 29 for pv magazine Webinar+ | Decoding the first massive cyberattack on Europe’s solar energy infrastructure – The Poland case and lessons learned
Industry experts will explore real-world cyberattack scenarios, highlight potential vulnerabilities in solar and storage systems, and share practical, actionable strategies to protect your energy assets. Attendees will gain valuable knowledge on how to anticipate, prevent, and respond to cyber threats in the rapidly evolving solar energy sector.
Operational modes
DDoS attacks can operate in volumetric mode, where large amounts of traffic flood network bandwidth, preventing legitimate communications from reaching their destination. Alternatively, they can function in application-layer mode, targeting specific services such as SCADA interfaces or monitoring application programming interfaces (APIs), overwhelming them with repeated requests that exhaust processing resources. In more advanced scenarios, protocol-based attacks exploit weaknesses in communication protocols to disrupt system functionality with relatively low traffic volumes.
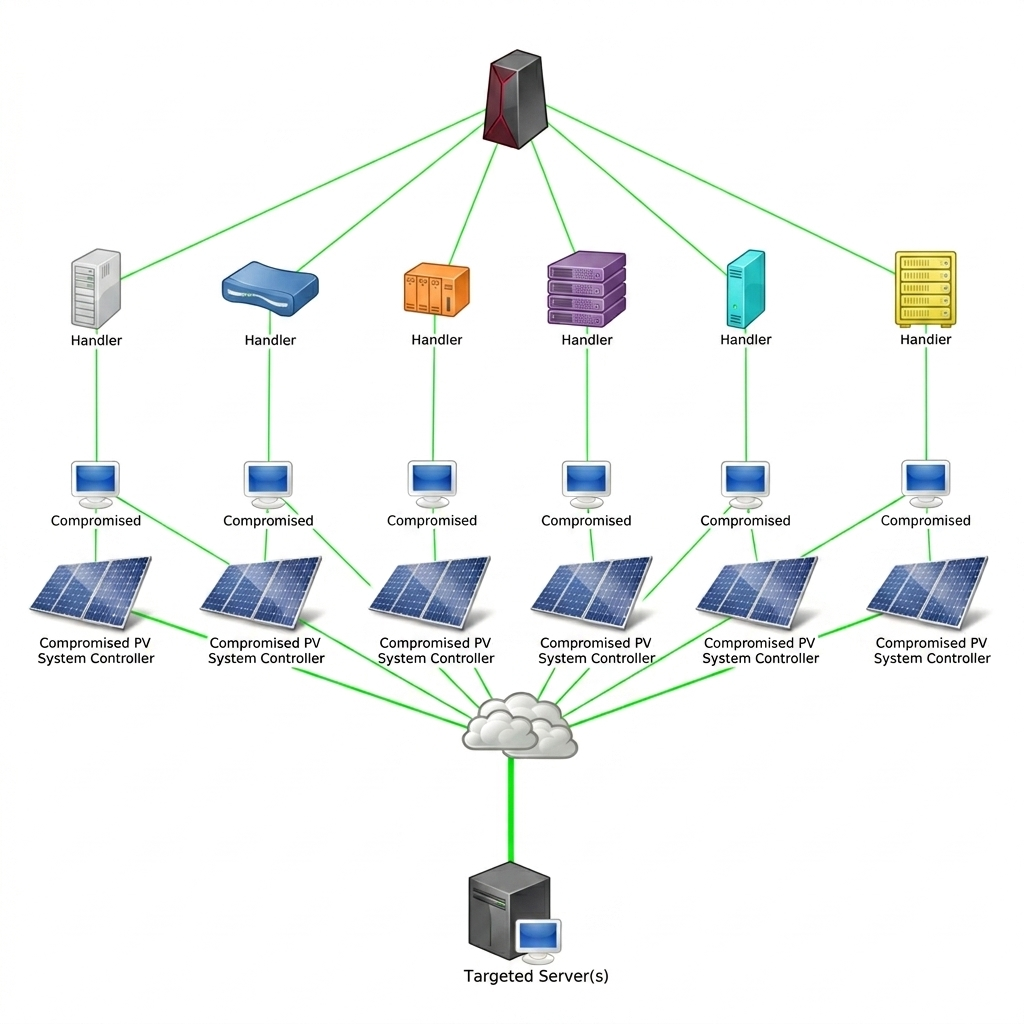
For PV systems, a DDoS attack typically begins with the attacker leveraging a botnet—a network of compromised devices—to generate traffic directed at critical components such as inverters, gateways, or cloud-based monitoring platforms. These attacks often exploit publicly exposed interfaces or weakly protected communication endpoints. Once initiated, the flood of traffic saturates network links or overloads system resources, preventing normal communication between devices.
Common techniques in PV environments include SYN floods, HTTP request floods, and amplification attacks that multiply traffic volume using misconfigured servers. In distributed solar fleets, attackers may also target centralized monitoring platforms, effectively blinding operators across multiple sites simultaneously.
Once the attack is underway, operators may notice delayed data updates, loss of remote control capabilities, or complete communication outages. At this stage, the attack is fully active, with the attacker maintaining pressure to prolong disruption. In prolonged attacks, recovery becomes more complex as systems may require manual intervention or staged restarts.
Defense
A potential defense against DDoS attacks in PV systems is to implement traffic filtering, rate limiting, and scalable network architectures that can absorb or deflect large volumes of malicious traffic. If these measures are applied, traditional tools like firewalls can become more effective by enforcing stricter traffic rules, blocking suspicious sources, and prioritizing legitimate communications.
Content delivery networks (CDNs) and DDoS mitigation services can also help by distributing traffic loads and filtering malicious requests before they reach critical infrastructure. Additionally, redundancy in communication channels ensures that if one path is overwhelmed, alternative routes can maintain system connectivity.
Standard network segmentation can also help protect PV systems from DDoS attacks by isolating critical components like inverters, SCADA systems, and monitoring platforms into separate zones. This limits the impact of an attack on any single segment. However, if key external interfaces remain exposed, attackers can still target entry points and disrupt essential services.
Intrusion detection systems (IDSs) can also help detect DDoS attacks in PV systems by identifying unusual traffic spikes, abnormal request patterns, or protocol misuse. They provide early warnings that allow operators to activate mitigation strategies. However, they cannot stop attacks on their own and must be integrated with automated response systems and traffic filtering mechanisms for effective protection.
Redundancy
In summary, DDoS attacks represent a serious risk to networked PV systems, primarily affecting their availability, operational continuity, financial performance, and overall cybersecurity posture. Although measures like traffic filtering, rate limiting, redundancy, network segmentation, firewalls, and IDS can help reduce the risk, none can fully protect the system alone.
Systems must be designed with redundancy, continuously monitoring traffic patterns, and deploying automated mitigation strategies.
This approach not only helps maintain system availability during an attack but also limits the attacker’s ability to sustain disruption or expand their impact across interconnected systems.
“DDoS attacks are not theory, they happen all the time. Looking at our sector, in a recent incident from 2024, the Japanese monitoring tool provider Contec announced 800 of its products were hijacked to form a DDoS botnet.” Sadot stated. “It is a relatively simple attack, but it can be damaging. Fortunately – mitigation and prevention tools are readily available.”
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.




By submitting this form you agree to pv magazine using your data for the purposes of publishing your comment.
Your personal data will only be disclosed or otherwise transmitted to third parties for the purposes of spam filtering or if this is necessary for technical maintenance of the website. Any other transfer to third parties will not take place unless this is justified on the basis of applicable data protection regulations or if pv magazine is legally obliged to do so.
You may revoke this consent at any time with effect for the future, in which case your personal data will be deleted immediately. Otherwise, your data will be deleted if pv magazine has processed your request or the purpose of data storage is fulfilled.
Further information on data privacy can be found in our Data Protection Policy.