Researchers at the University of Belgrade in Serbia have compiled a global dataset of all reported cybersecurity threats and incidents affecting energy infrastructure and have found that European Union and BRICS are the most impacted, followed by the United States.
The dataset relates to the 2022-2024 period and includes all cyber attacks perpetrated to either power plants, oil and gas infrastructure, as well as nuclear plants and and district heating networks.
“Unlike most existing works, this study has adopted a broader approach by employing an integrated review, incorporating grey literature as an important source for building the dataset. The use of grey literature was motivated by the aim of collecting information on the most recent incidents,” the scientists said.
Grey literature encompasses research and information produced by governments, academic institutions, businesses, and industry that is not managed or published through commercial channels.
Join us on Apr. 29 for pv magazine Webinar+ | Decoding the first massive cyberattack on Europe’s solar energy infrastructure – The Poland case and lessons learned Industry experts will explore real-world cyberattack scenarios, highlight potential vulnerabilities in solar and storage systems, and share practical, actionable strategies to protect your energy assets. Attendees will gain valuable knowledge on how to anticipate, prevent, and respond to cyber threats in the rapidly evolving solar energy sector. Overall, the dataset comprises 119 incidents, of which 53 occurred in 2022, 27 in 2023, and 39 in 2024. The attacks targeted the energy infrastructure of some of the world’s largest companies, including Finland’s Fortum, Spain’s Repsol and Iberdrola, Italy’s Eni and Acea, France’s Engie, Israel Electric Company, Russia’s Gazprom, Lukoil, and Rosneft, Estonia’s Eesti Energia, Greece’s Public Power Corporation (PPC), India’s Tata Power, Taiwan’s Taipower, Ukraine’s Oblenergo, South Africa’s Eskom, and US-based Devon, among many others, including smaller energy firms. One notable incident involved the Italian energy agency, Gestore dei Servizi Energetici (GSE), which plays a central role in regulating and supporting the renewable energy market as a state-owned entity under the Ministry of Economy and Finance. GSE administers incentive schemes, allocates public funding, and oversees access procedures for renewable support, while ensuring compliance with regulations. The research categorizes cyber incidents into three types: distributed denial-of-service (DDoS) attacks, which overwhelm systems or networks to disrupt access; ransomware, where attackers block resources and demand payment to restore access or protect data; and malware, encompassing any malicious software that compromises a system’s security, confidentiality, integrity, or availability. Motives are classified as financial or political, with political motives including espionage, sabotage, and hacktivism, which the scientists describe as ideologically driven political discrediting. The dataset shows that in 2022 most cyber incidents occurred in EU and BRICS countries, led by Russia and Germany, with notable impacts in Eastern and Southeast Europe and Central Asia. In 2023 and 2024, the focus shifted to North America and Asia, with the United States as the most affected country and Israel emerging as a key target. Overall, the geographic pattern moved from Europe and BRICS toward North America and Asia over the three years. Image: “The power sector dominated among the most affected sub-sectors with 36% of incidents recorded, followed by the oil sector and the natural gas sector, accounting for 25% and 23%, respectively,” the researchers noted, without providing data separating renewable and conventional power infrastructure. “Taking into consideration 8% of incidents in the nuclear sector alone, it additionally reinforces the impression of the power sector's attractiveness and vulnerability, accounting for 44% in total.” The dataset also shows that financially motivated attacks focused on power (37%), natural gas (32%), and oil (28%), mainly in North America and Europe, while politically motivated attacks were dominated by hacktivism (47%), followed by espionage (36%) and sabotage (16%), often linked to geopolitical conflicts. Ransomware was the most common attack type (51%), primarily causing data theft, while malware (17%) targeted both operations and data. All types of threat actors were involved, including cybercriminals, hacktivists, espionage groups, and national cyber armies. “The research demonstrates that all types of threats are simultaneously present, increasing in intensity, sophistication, and impact potential,” the research group emphasized. “The cyber threat landscape is characterized by a diverse set of actors, including state-sponsored groups, cybercriminals, and hacktivists, often with overlapping agendas and motivations ranging from financial gain to political leverage, geostrategic and industrial competition, and physical disruption.” “It is also noticeable that although financial motivation still dominates attacks, incidents increasingly have a certain political connotation due to geopolitical rivalry and armed conflicts,” the academics concluded. “This is evident in increasingly frequent extensive espionage campaigns or the creation of sophisticated, specially designed tools capable of inflicting far-reaching consequences.” The dataset was presented in “Cyber threats and energy security: Development and analysis of an incident dataset for the period 2022–2024,” published in Energy Policy. This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.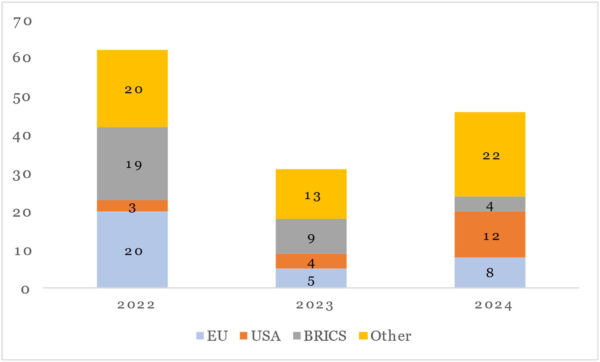
University of Belgrade, Energy Policy, CC BY 4.0




By submitting this form you agree to pv magazine using your data for the purposes of publishing your comment.
Your personal data will only be disclosed or otherwise transmitted to third parties for the purposes of spam filtering or if this is necessary for technical maintenance of the website. Any other transfer to third parties will not take place unless this is justified on the basis of applicable data protection regulations or if pv magazine is legally obliged to do so.
You may revoke this consent at any time with effect for the future, in which case your personal data will be deleted immediately. Otherwise, your data will be deleted if pv magazine has processed your request or the purpose of data storage is fulfilled.
Further information on data privacy can be found in our Data Protection Policy.